Oops! Microsoft Lets Its SSL Certificate Expire Causing a Major Outage
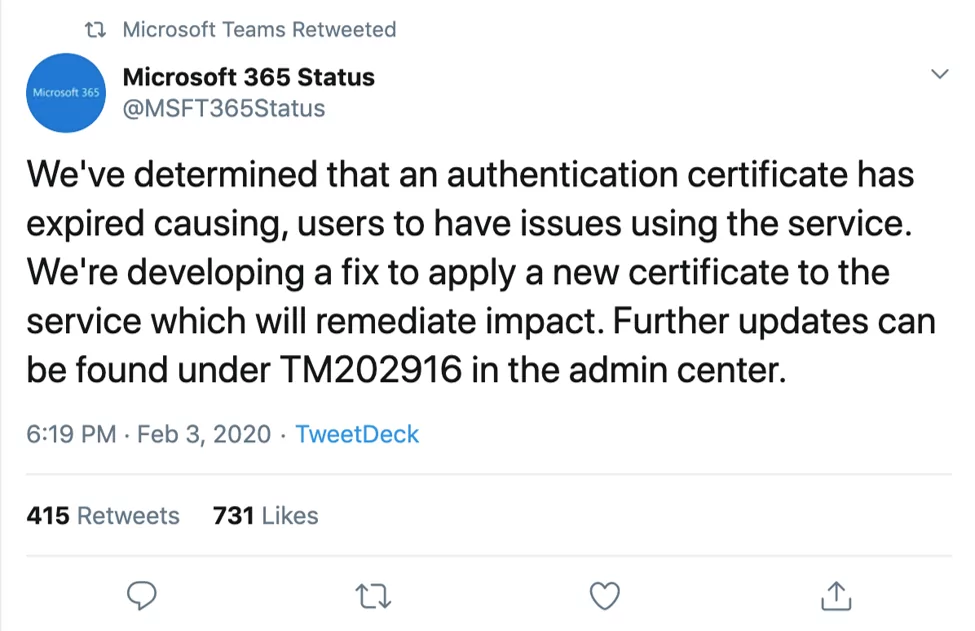
On February 3rd, Microsoft Teams suffered outages following the expiration of one of its SSL certificates. Microsoft’s collaborative Slack-alike, Teams, bundles together a variety of Microsoft applications having over 20 million daily active users. This is not the first outage case for online giants (remember Instagram and Google) and probably will not be the last.
Unlike other services that renew automatically, SSL Certificates have a set expiry date. Letting an SSL Certificate expire can have inevitable consequences for the organization and also for the visitors or users. In 2017, Equifax, which gathers consumers’ credit histories, revealed a massive security breach compromised the personal information of about 150 million people due to forgotten certificate expiration.
This case demonstrates why keeping in control of certificates is so important. While Microsoft has thousands of certificates to keep track of, outages like yesterday’s confirms that it just takes one expiry to cause major outages. To stay in the safe side, organizations should look to automate the discovery, management and replacement of every single certificate on its network.
Here’s 3 actionable advices on avoiding SSL certificate expiry incidents:
- Search for the deep cause of the problem: the vast complexity of modern IT architectures which requires an increasing number and variety of digital assets requiring continuous visibility.
- Although it’s sometimes perfectly useful, don’t trust on legacy scripts which can not receive support from its developer. SSL infrastructure is an important part of your security infrastructure that needs to be handled from risk compliance perspective.
- Make sure the platform not only finds and monitors SSL certificates for expiration dates but also for possible vulnerability issues and track rogue certificates by checking certificate transparency logs.
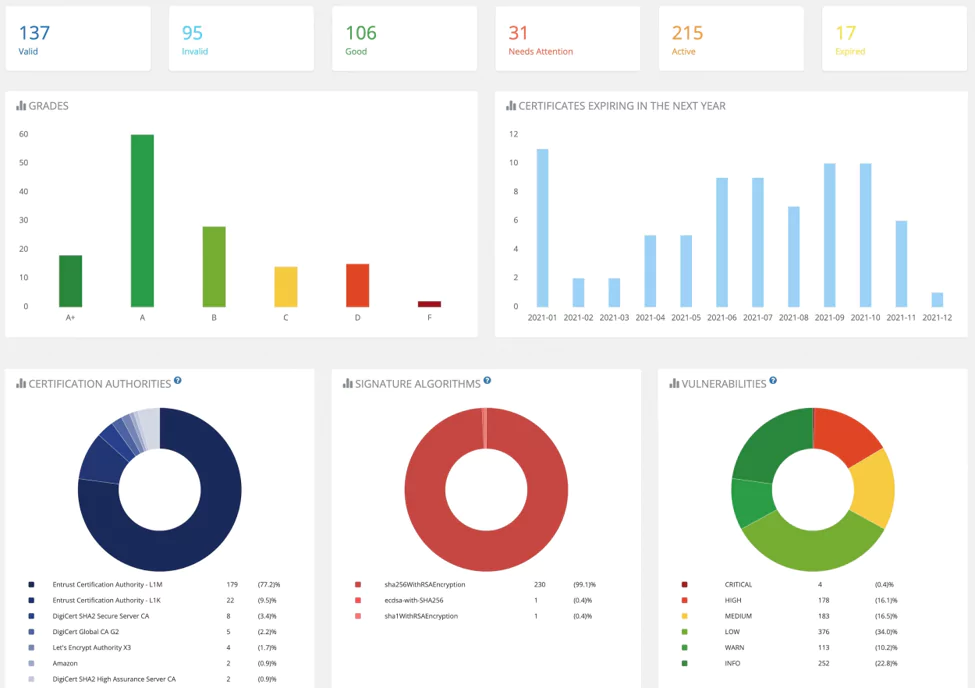
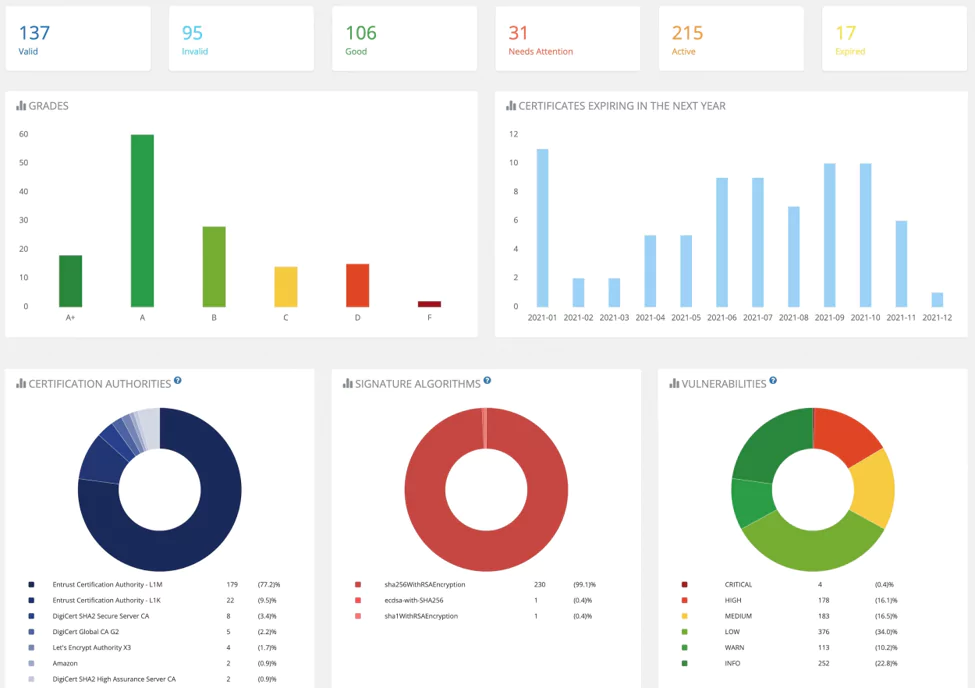
Image 2. SOCRadar’s SSL Certificate Management Dashboard
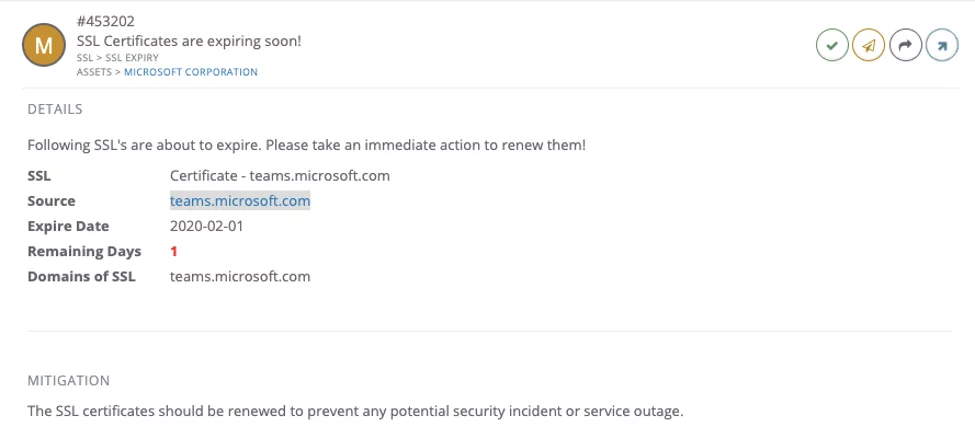
Image 3. Sample SOCRadar alert on SSL certificate expiry
Within the SOCRadar Digital Risk Protection platform, customers can hover over the graphs on the SSL Certificates page to see the percentage of an organization’s SSL certificates by certification authorities, signature algorithms, vulnerabilities, grades, or expiration dates. The reason for each certificate’s grade is provided, so it is much easier for SOC teams to fix problems with their certificates and improve their overall security posture.
Also, see: